I’ve been doing this long enough to remember when a zero-day was something whispered about in conference hallways (I know I’m old). A rare, expensive, almost mythological artifact, the kind of thing nation-states hoarded, and intelligence agencies paid seven figures to acquire. The barrier to weaponizing a zero-day used to be something…you needed time, expertise, […]
What Zero Trust Actually Requires That Nobody Wants to Talk About
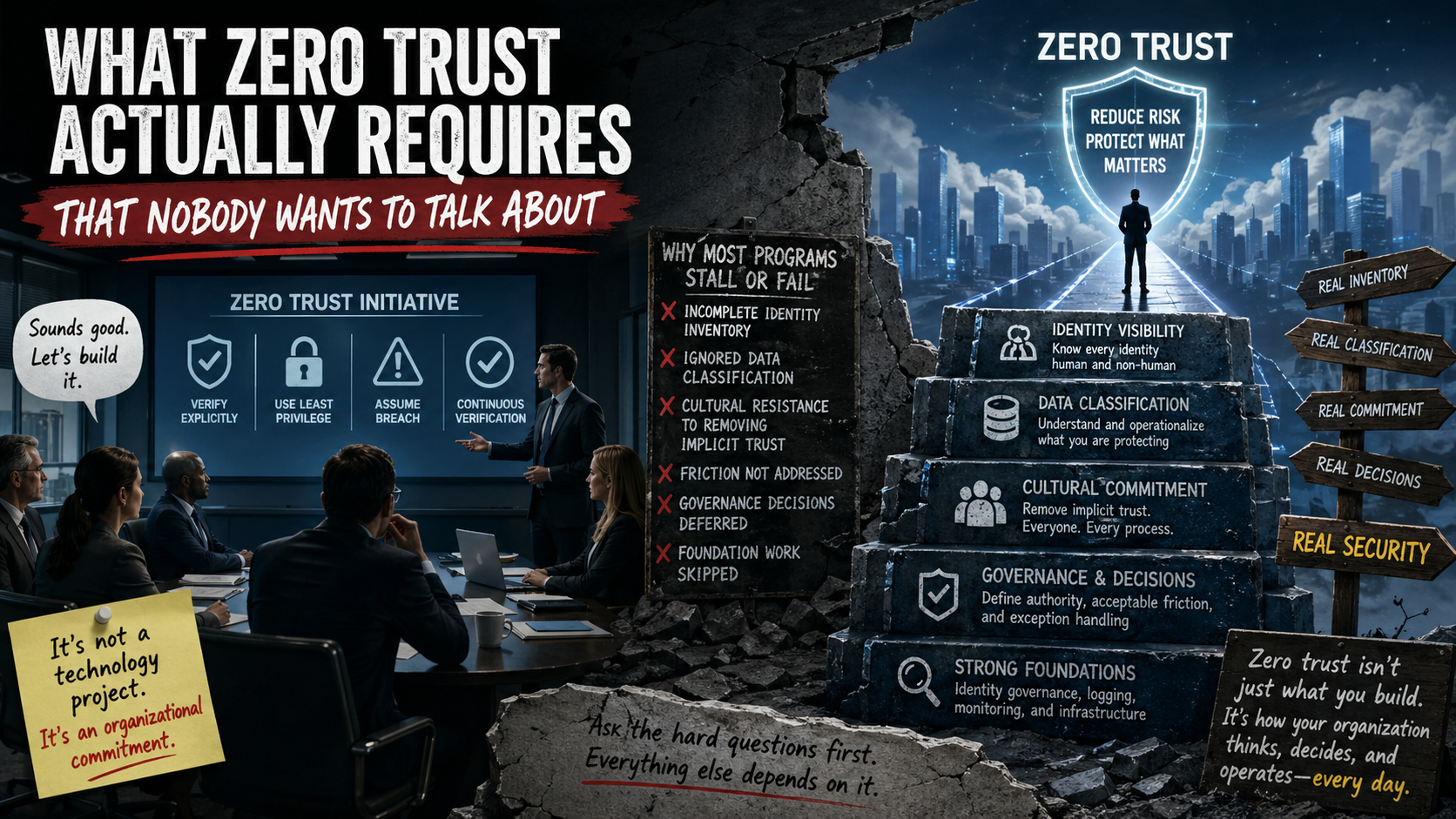
Am I the only one who has experienced this…usually after a board meeting or a vendor briefing, where someone announces that the company is going to implement zero trust. The room nods, a working group gets formed, budget line appears and within a few weeks, the initiative is underway… with everyone quietly assuming that what […]
Why Detection Without Understanding Is Just Noise
Most security operations environments that I have had the luck of seeing, look impressive. They have dashboards everywhere, there are alerts firing and their SIEM is lit up like it’s doing something meaningful. From anyone on the outside, it reads as a mature, well-instrumented program. From the inside…if you’re really honest about it, is a […]
Ownership was Assigned….accountability is another story
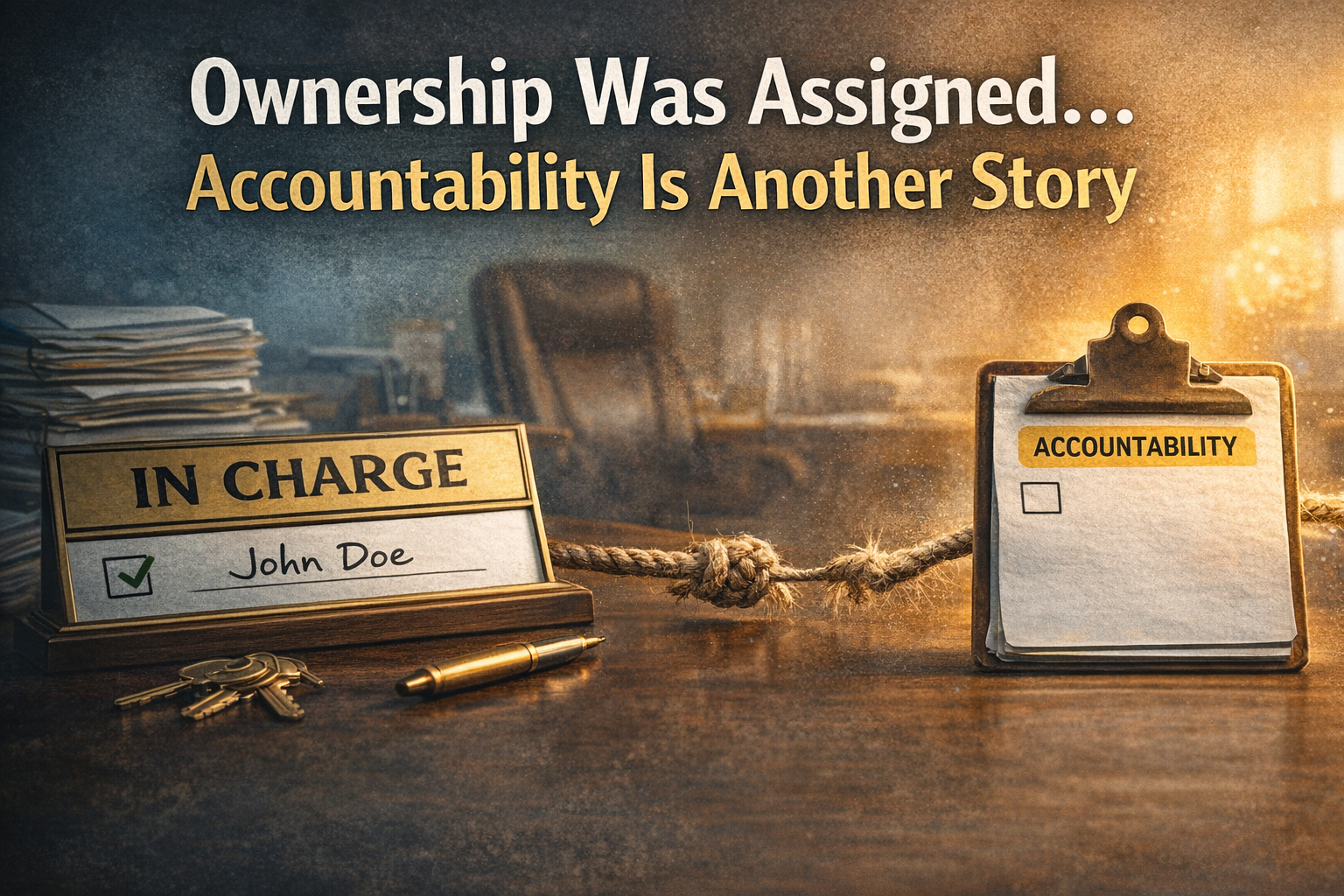
There is a conversation that happens in almost every organization I have ever encountered, usually in a conference room, usually after something has gone sideways, backward and upside down. Someone of extreme importance asks who owns a particular system, process, or risk. There is almost always a pause… that lasts just long enough to become […]
Your Security Program Looks Great… For the Audit

I feel like we all have that moment in our security programs maturation when things start to feel… comfortable. The dashboards look clean, the controls are documented, the audit findings are minimal and most importantly (in some people’s opinions) the reports are polished. Everything appears to be working as intended. That is the exactly the […]
Not Every Manager Is a Leader (And That’s the Problem)
I had the opportunity to have a run in with an old colleague (he’s not old, we’ve just haven’t seen each out in a while) and we got to talking about everything that has been going on in our lives since we’ve parted and talk eventually made its way into the problems with not being […]
When Security Architecture Depends on Tribal Knowledge
There is a moment in almost every organization when someone says a phrase that sounds reassuring on the surface but I hope should make security leaders just a little uncomfortable: “Don’t worry, Mike knows how that works.” (no real Mike’s are used in today’s example). Mike I’m sure is a great guy, he’s been with […]
The Security Implications of Over-Automation

Not long ago I was in a conversation with a few other security leaders about automation. It started the way these conversations often do, someone mentioned how much faster their team was able to respond to alerts since implementing automated workflows. Another person talked about automatically isolating compromised endpoints upon alerts and someone else described […]
The Silent Risk of Inconsistent Time Synchronization

If you’ve been in any level of incident response, there is a moment in the conversation when someone asks a deceptively simple question: “When did this start?” It sounds like a straightforward request…after all, security teams collect logs, alerts, and telemetry from systems across the organization. We have dashboards, SIEMs and sometimes monitoring platforms that […]
The Hidden Risk in Identity Lifecycle Gaps

There is a moment in almost every security program where someone confidently says, “We have a solid joiner, mover, leaver process.” It usually comes up in audits, board discussions, or when someone is explaining how identity is clearly under control. On paper, it looks great. New employees get access based on role. Transfers trigger updates. […]

Recent Comments