Am I the only one who has experienced this…usually after a board meeting or a vendor briefing, where someone announces that the company is going to implement zero trust. The room nods, a working group gets formed, budget line appears and within a few weeks, the initiative is underway… with everyone quietly assuming that what […]
Shadow Access: The Security Risk You Don’t See Until It’s Sitting in the Boardroom With You
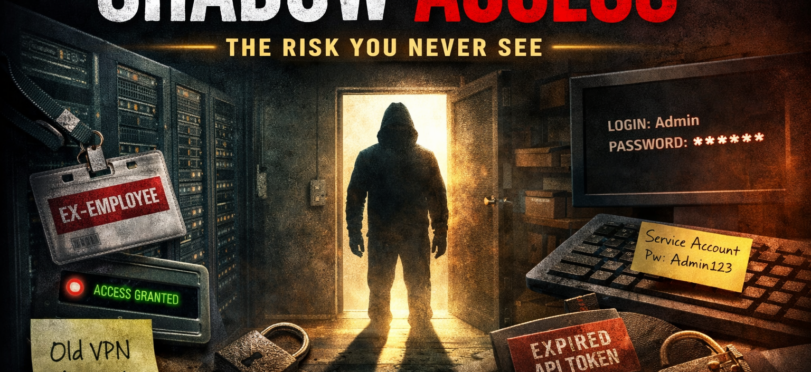
After 20 plus years in technology and security, I’ve learned something important…well learned a lot of important things…but this is the one I’m writing about The biggest risks that we have that we aren’t aware of rarely come crashing through the front door, they slip in quietly because they already have access and no one […]
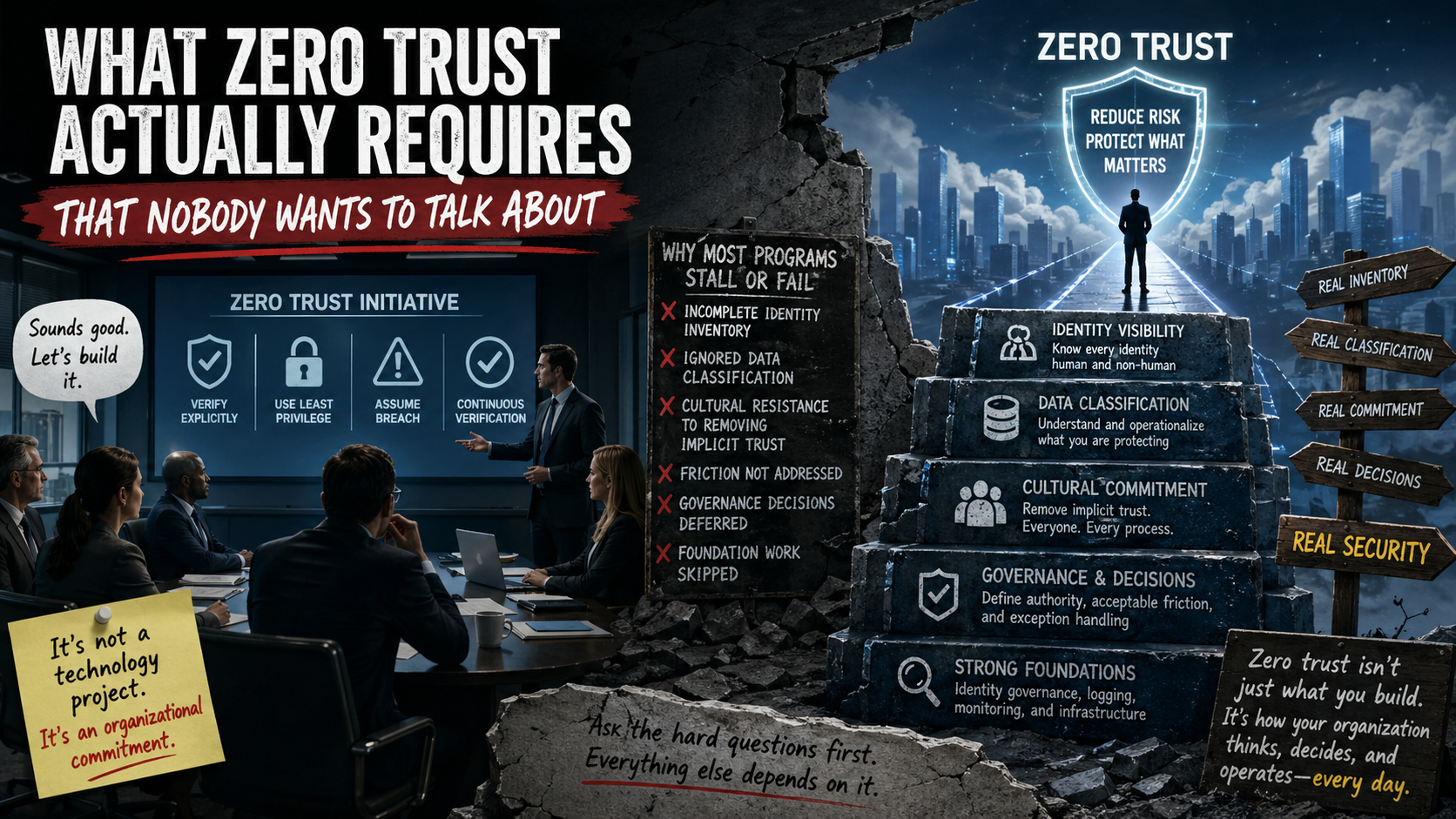
How to implement Zero Trust
After answering the question from Monday I kept thinking of how the best way to start programs from scratch. One method I usually recommend is a Zero Trust security model. Now the thing I run into when talking about this, is that people think it’s an all or nothing approach, and most have many issues […]
Recent Comments