After 20 plus years in technology and security, I’ve learned something important…well learned a lot of important things…but this is the one I’m writing about
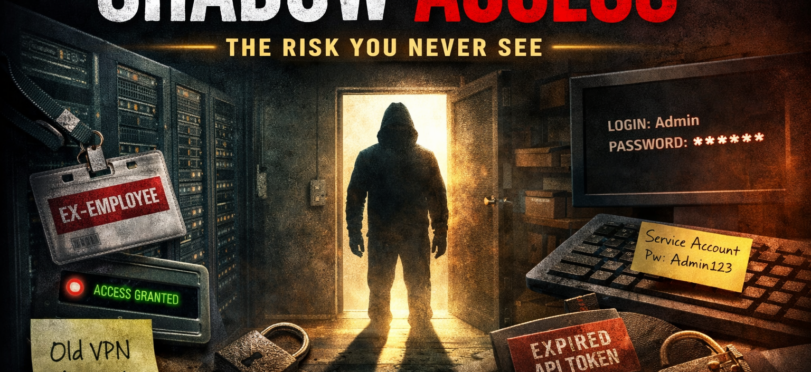
The biggest risks that we have that we aren’t aware of rarely come crashing through the front door, they slip in quietly because they already have access and no one remembers giving it to them.
That risk is shadow access.
Not shadow IT. That gets all the headlines. Shadow access is sneakier, quieter, and far more dangerous. If shadow IT is someone bringing their own coffee maker into the office, shadow access is someone still having keys to the building long after they stopped working there. And yes, it happens more often than anyone likes to admit.
What Is Shadow Access, Simply Put
Shadow access exists when users, accounts, or systems have access they should not have, no longer need, or were never supposed to have in the first place. The access might have been legitimate once. That’s what makes it dangerous. This is not hacking. This is leftovers we’ve forgotten about and they aren’t tasty.
There maybe popular examples you’ve probably seen in the news (or at work):
- A former employee whose VPN still works
- A contractor account that was “temporary” three years ago
- A service account with admin rights and no clear owner
- API tokens created for testing that accidentally made it into production
- Elevated access granted during an incident or for installations and never rolled back
No alarms go off. No malware is involved. Everything looks normal. Which is exactly the problem. Shadow access is rarely caused by negligence. It’s caused by speed, pressure, and good intentions. Someone needed access quickly. A system was down. A project had a deadline. A vendor needed to troubleshoot a critical (or not so critical) problem.
So access was granted, And then life happened. People changed roles. Projects ended. Vendors rolled off. Documentation fell behind and yet the access stayed. We’ve all heard of technical debt, but rarely hear anyone talk about access debt and just like technical debt, it compounds quietly until one day it becomes very expensive.
One of the most common sources of shadow access that I’ve seen is role creep. An employee starts in Role A. They move to Role B. They help out temporarily with Role C. No one removes Role A or B because “they might need it again.” or still use it during their transition. Six years later that user effectively has the permissions of three jobs.
No one intended to create a superuser. It just happened. From a security standpoint, this breaks the principle of least privilege. From an audit standpoint, it breaks everything else.
Malicious actors are not always looking to break in through the front door, sometimes they just look around for open doors and shadow access is attractive because:
- The credentials are valid
- The accounts can often bypass MFA (think service accounts)
- Activity looks legitimate
- Logging is minimal or nonexistent
- No one actively monitors usage
If an attacker compromises a forgotten account, they may not need to escalate privileges, because the privileges are already there. This is why many breach investigations eventually include the sentence: “The account was legitimate but should not have existed.” That sentence never makes anyone feel better.
Why Executives Should Care
From a leadership perspective, shadow access is not a technical issue, it’s a governance issue.
It can impacts:
- Regulatory compliance
- Audit outcomes
- Incident response containment
- Cyber insurance discussions
- Board reporting confidence
When an executive says, “Who had access to this system,” the worst possible answer someone can give is, “We’re not entirely sure.” That uncertainty erodes trust faster than any vulnerability scan.
This is not new wisdom, or atleast shouldn’t be. Most major frameworks quietly emphasize this risk.
- NIST CSF speaks to identity governance, access control, and lifecycle management
- Zero Trust assumes access must be continuously validated, not permanently granted
- ISO 27001 requires periodic access reviews and ownership
- SOC 2 expects documented provisioning and deprovisioning
- CIS Controls call out account management as foundational
Yet many organizations treat access reviews as a checkbox exercise, a quarterly or yearly email. A few clicks. Approve all. Move on. That is compliance theater and shadow access thrives in this theater.
Let’s talk honestly, why our reviews fail. Most access reviews fail for predictable reasons:
- Managers don’t understand what access actually means, so it’s easier to just click approve.
- Reviews contain hundreds of entitlements with cryptic names that no one understand.
- Business owners are afraid to remove access “just in case” the user needs it at some point.
- No one wants to be responsible for breaking something.
So the safest choice becomes approval, system is not secure, just safe politically and that’s how shadow access survives every review cycle.
We’ve talk about employee access is messy, now let’s talk about how service accounts are pure chaos.
Many environments have:
- Service accounts created by vendors
- Credentials embedded in scripts
- Passwords that never expire
- No MFA
- No owner
- No monitoring
These accounts often have broad permissions because “the application needs it.” and it’s easier to give the rights than test them. Maybe it does. Maybe it doesn’t or no one remembers why it has that anymore. From a malicious actor’s point of view, this is like finding a master key under the welcome mat.
Here’s the uncomfortable truth that we need to really understand, shadow access is rarely solved by buying another tool. You can have A modern IAM platform, Privileged access management, Single sign on, Conditional access and all the Fancy dashboards and still have shadow access everywhere.
Because this is a process and mindset problem first. Now tools can help enforce discipline but they do not create it.
What can you do to mature your program
Organizations that manage shadow access well tend to share a few behaviors to incorporate.
1. Identity as the source of truth
HR events drive access. Not emails. Not hallway conversations. Joiner, mover, leaver processes are automated and enforced.
2. Ownership is mandatory
Every account has a clearly defined owner and no owner means no access. Yes, that includes service accounts.
3. Access is time bound
Elevated access expires automatically and If you still need it, request it again. Temporary should actually mean temporary.
4. Reviews focus on removal, not approval
The goal of access reviews is not to confirm everything is fine, the goal is to remove what is not needed. That mindset shift alone changes outcomes.
5. Logging and alerting on dormant access
Accounts that never log in should raise questions and reviews. Silence from an account is not safety (well at least for long)
The Cultural Shift That Actually Matters
The biggest change is cultural, we often forget that in our tooling and policies are not the end of the conversation, but an education tool. You organizations must move from “Who might need access someday” to “Who needs access right now” and that sounds subtle. It’s not.
One mindset creates accumulation. The other creates real control. Security maturity is not about denying access It’s about intentional access. Every permission should have a reason, an owner, and an expiration and if it doesn’t, it becomes shadow access by default.
The Question Leaders Should Be Asking
If you are an executive or security leader, here is a simple but powerful question to ask your team:
“Can we confidently explain who has access to our most critical systems and why?”
Not eventually. Not after an audit. Not once we clean things up…right now. If the answer includes long pauses, caveats, or nervous laughter, you’ve found your next priority. The truth is, we all need to grow here.
Finally
Shadow access does not announce itself. It does not generate alerts. It does not appear on dashboards. It waits. Then when something goes wrong, it suddenly becomes the center of the conversation. The goal is not perfection. The goal is visibility, ownership, and intention. Remember access you don’t understand is access you don’t control and access you don’t control is risk you’re already carrying.
Thoughts
Here’s the real question I’ll leave you with is…
When was the last time your organization removed access instead of approving it?
I’d love to hear how others are tackling shadow access, especially what has actually worked and what turned into a painful lesson learned.
Drop your thoughts below.