I’ve been doing this long enough to remember when a zero-day was something whispered about in conference hallways (I know I’m old). A rare, expensive, almost mythological artifact, the kind of thing nation-states hoarded, and intelligence agencies paid seven figures to acquire. The barrier to weaponizing a zero-day used to be something…you needed time, expertise, […]
What Zero Trust Actually Requires That Nobody Wants to Talk About
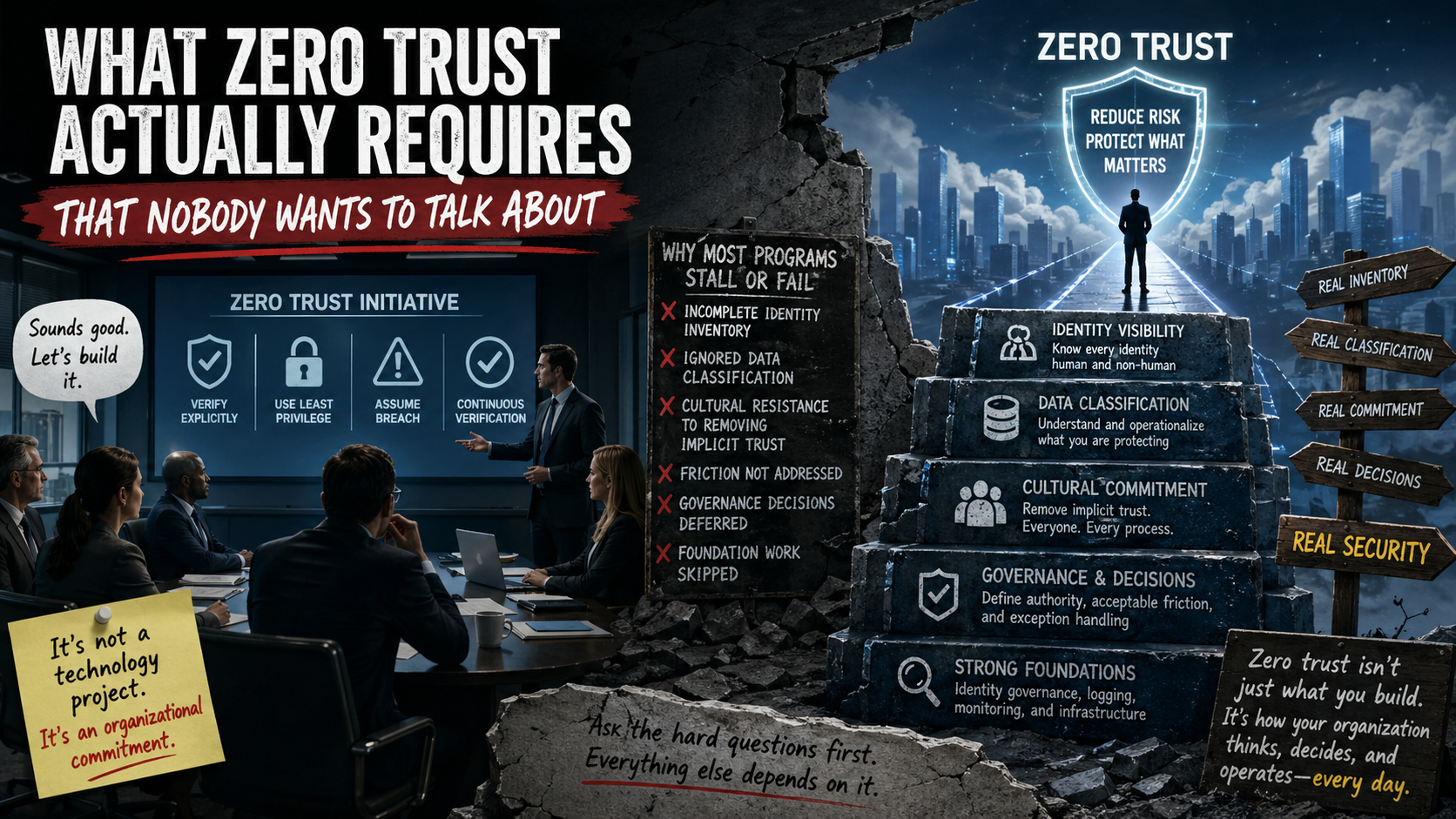
Am I the only one who has experienced this…usually after a board meeting or a vendor briefing, where someone announces that the company is going to implement zero trust. The room nods, a working group gets formed, budget line appears and within a few weeks, the initiative is underway… with everyone quietly assuming that what […]
Why Detection Without Understanding Is Just Noise
Most security operations environments that I have had the luck of seeing, look impressive. They have dashboards everywhere, there are alerts firing and their SIEM is lit up like it’s doing something meaningful. From anyone on the outside, it reads as a mature, well-instrumented program. From the inside…if you’re really honest about it, is a […]
Your Security Program Looks Great… For the Audit

I feel like we all have that moment in our security programs maturation when things start to feel… comfortable. The dashboards look clean, the controls are documented, the audit findings are minimal and most importantly (in some people’s opinions) the reports are polished. Everything appears to be working as intended. That is the exactly the […]
When Security Architecture Depends on Tribal Knowledge
There is a moment in almost every organization when someone says a phrase that sounds reassuring on the surface but I hope should make security leaders just a little uncomfortable: “Don’t worry, Mike knows how that works.” (no real Mike’s are used in today’s example). Mike I’m sure is a great guy, he’s been with […]
The Security Implications of Over-Automation

Not long ago I was in a conversation with a few other security leaders about automation. It started the way these conversations often do, someone mentioned how much faster their team was able to respond to alerts since implementing automated workflows. Another person talked about automatically isolating compromised endpoints upon alerts and someone else described […]
Shadow Access: The Security Risk You Don’t See Until It’s Sitting in the Boardroom With You
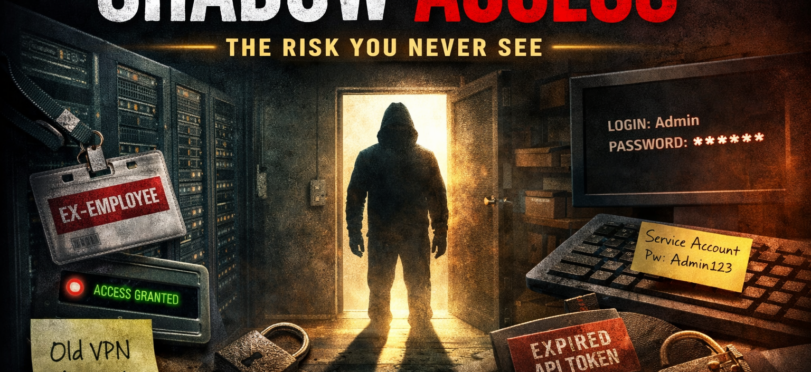
After 20 plus years in technology and security, I’ve learned something important…well learned a lot of important things…but this is the one I’m writing about The biggest risks that we have that we aren’t aware of rarely come crashing through the front door, they slip in quietly because they already have access and no one […]
Securing Beyond the Standard: Building a Culture of Lasting Security

AI Generated
Mastering the Art of Communicating Your Security Success
While there is great value in the work that security professionals do every day, but communicating that success is key to helping build knowledge about what and how your program is doing. However, demonstrating the effectiveness of your cyber security measures to stakeholders—be they executives, employees, or clients—can be challenging. Here’s some thoughts on effectively […]
Helping Your Users Stay Safe Online Helps to Keep the Office From Catching Fire (You Know…Metaphorically Speaking)

I have rarely seen any Cyber Security Awareness Training at any company, explaining how I can take care of my assets, how I can avoid falling for scams or other things to help my browsing online. Now for me, that’s not a problem, I’ve been in IT and Information Security my whole life, and I’m cautious when I’m online at home or work, but I want to talk about why I would like that to change. Why training employees to be more suspicious online, can and will help them to be better at work.

Recent Comments